Contents
About TOR Browser
There are many ways in which the internet can track us. By using our IP address, websites were able to use identifiable information to target advertising and collect data about our browsing habits.
It is why Activists, Journalists, and privacy advocates are leaning towards an anonymous browser like Tor. You don’t have to be a criminal or hacker to want to stay anonymous online.
In a normal internet connection, you are directly connected to a website you are trying to visit. This website and any other prying eyes can see who you are and that you are trying to access their server by using your IP address.
Tor is a web browser that is used to browse the web anonymously. The TOR network is made up of countless nodes or relay points that pass your data on passing through layers of encryption. And hence the onion metaphor. The TOR network is designed so that no server can know who you are or what you doing.
Each node that your data passes through peels off another layer of encryption showing the previous node’s IP address as well as where it has been sent to. The last node your data passes through is called the Exit node and it peels off the final layer of encryption and delivers your data to the intended server.

The point of origin and the intermediate nodes are completely unknown to each other. And when you are finished with your browsing session, the TOR browser would invalidate all your cookies, browsing history, and other data.
Besides browsing the internet, TOR users can utilize its hidden services to create private websites and communication tools that can be only found using the TOR browser.
These private sites which are part of the dark web are the black markets that can be found.
Not all activities on the TOR are for illegal purposes. Anonymous internet usage is important for Journalists who are reaching out to sources, activists who are in a country where the sensor or blocked internet. And even law enforcement officers who use it for undercover operations.
How to Use TOR Browser?
- Go to the TOR download page.
- https://www.torproject.org/download/
- If you are not able to open the above link, then you have to connect through any VPN.
- Select the appropriate operating system of the device and download the installation file.
- Execute the installer and extract the TOR browser to a folder.
- Then just open the extracted folder and start the TOR browser.
- If it shows options to connect or configure, select connect.
- To make sure you are connected to the TOR network, go to check.torproject.org. It should show a success message.
Every time you open the TOR browser, a new identity will be created for you. In case you want to stop previous browser activity and create a new identity, there is an option called New Identity under Menu. When you create a new identity, it will close all your current tabs, clear your cookies as well as your browsing history.
Different Security Levels in TOR
Without using safety settings in TOR, your data is vulnerable to prying eyes. Click on the shield icon to change the security level.
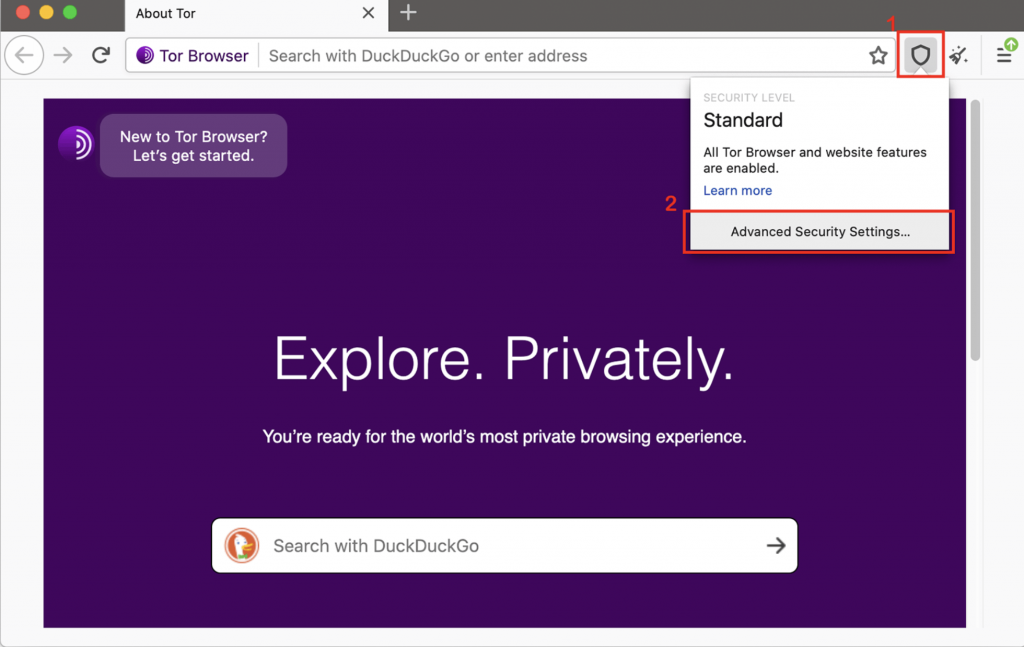
There are three security levels designed in the TOR browser.
-
Standard
Standard denotes the browser will allow all the features like Javascript, downloads. You will able to see websites fluidly. In standard mode, the page may load faster. You will be able to view websites properly without any issues in this mode.
-
Safer
The next security level is the Safer. In this mode, the browser will limit some functionalities. JavaScript will be allowed only on HTTPS sites. Some symbols and fonts will be disabled in this mode. The user needs to click-to-play on Audio and Video. This mode is recommended as it will allow most websites to function properly.
-
Safest
The last security level is the Safest. This is the safest among the three levels. But this limits most of the functionalities in the browser. Javascript will be disabled by default on all websites. The user needs to click-to-play on Audio and Video. Apart from symbols and fonts, icons and images will be disabled. Most of the websites will fail to open in this mode. This mode also delays the page loading time. If you face page loading issues, you have to change back to Safer or Standard mode.
Avoid Extensions/Add-ons in TOR
Installing browser extensions has become a habit for most of us. Browsers are small programs of different kinds. It can be an adblocker in the front and collect your activity in the background.
Installing add-ons on TOR is similar to using any conventional browser. It throws privacy and security at stake. Every browser has something called Browser Fingerprinting which keeps tracking the user across the internet. This is a way of profiling a user based on his browsing habits. The add-ons can be maliciously designed to target a user and share sensitive data.

Tor browser already comes with 2 pre-installed add-ons namely NoScript and HTTPS Everywhere.
Conclusion
Nothing is perfect. While the onion router makes it harder for hackers and spies to track your activity, it doesn’t make it impossible. There are still ways attackers can view activity on the network and extract data from vulnerable entry and exit points.
So should you use the TOR to browse the internet? If you are a casual internet user and signing on to Facebook or Twitter, probably not, because you are already putting your identity anyway. But if you are looking to score some weed and read ProPublica, well then you should use TOR.

As an extra level of security, we recommend you connect through any VPN, so that any entry and exit node won’t have an option of exposing your real IP address at any point.
